Strategic National Infrastructure Research
Beyond participating in public bug bounty platforms, I proactively dedicate my expertise to strengthening Indonesia's national digital defense. Through responsible disclosure, I have successfully identified and assisted in the remediation of 130+ validated vulnerabilities across 100+ national strategic entities.
Disclosure & Integrity Policy
To uphold the principles of National Cyber Resilience, I maintain strict confidentiality regarding the identities of these institutions. All findings are reported through the National Cyber and Crypto Agency (BSSN) or respective CSIRT teams. My primary objective is the silent and effective remediation of vulnerabilities to protect national data integrity.
* Data is manually aggregated and maintained for accuracy (approx. 98%+ precision).
DETAILED TRIAGE LOGS (PUBLIC PROGRAMS)
Sensitive Data Exposure > Disclosure of Secrets
HSBC (Bugcrowd)Successfully identified the exposure of sensitive credentials within the application scope. The security team triaged the report as technically valid.
[+] VIEW VALIDATION LOG
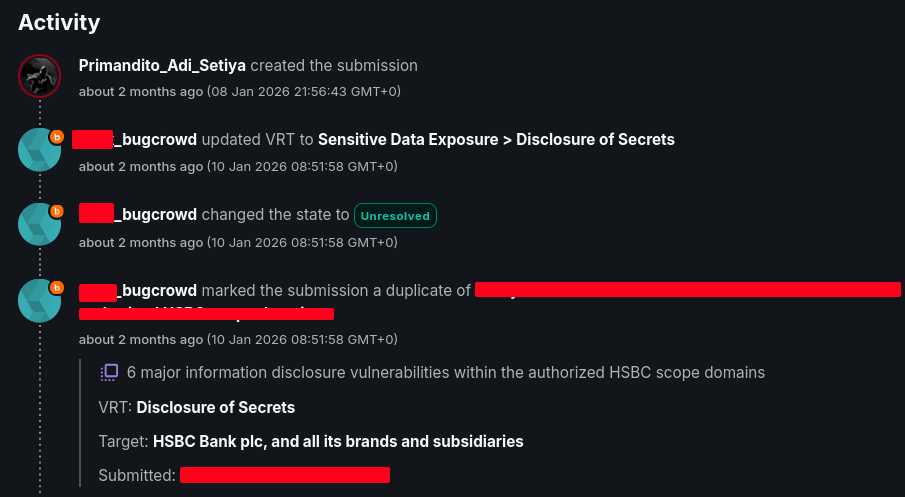
Screenshot: Triage acknowledgement and status assignment.
Information Disclosure
NokiaDetected an information leakage vulnerability revealing internal system configurations. The finding was acknowledged by the security team as valid research, demonstrating effective reconnaissance on the target infrastructure.
[+] VIEW VALIDATION LOG
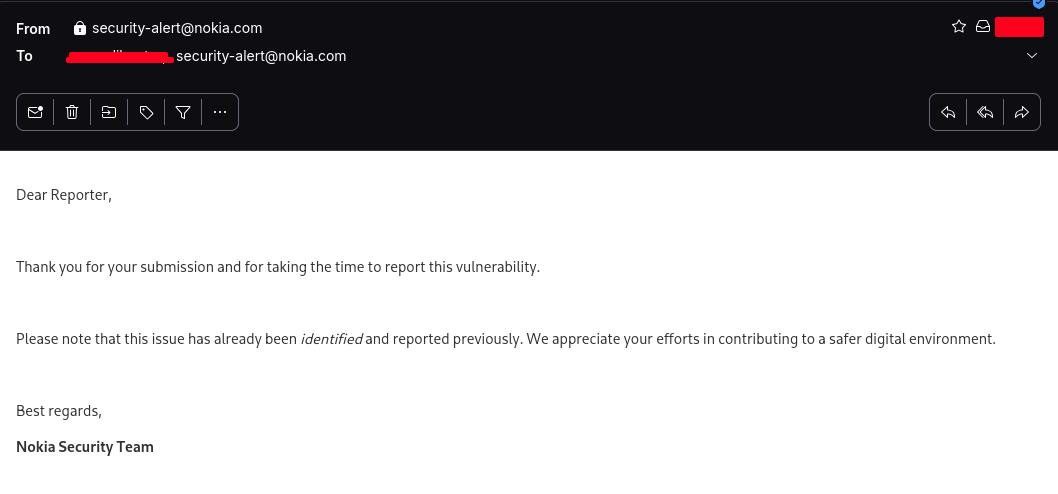
Screenshot: Validated duplicate report activity.
Information Disclosure > Leak of Client Configuration & Secrets
Kaseya (Inky)Identified a sensitive configuration exposure within a Keycloak instance. The research detailed a vulnerability chain where leaked client secrets and an insecure CORS policy could be leveraged for authenticated data exfiltration. The finding was confirmed as technically valid and passed preliminary review.
[+] VIEW VALIDATION LOG
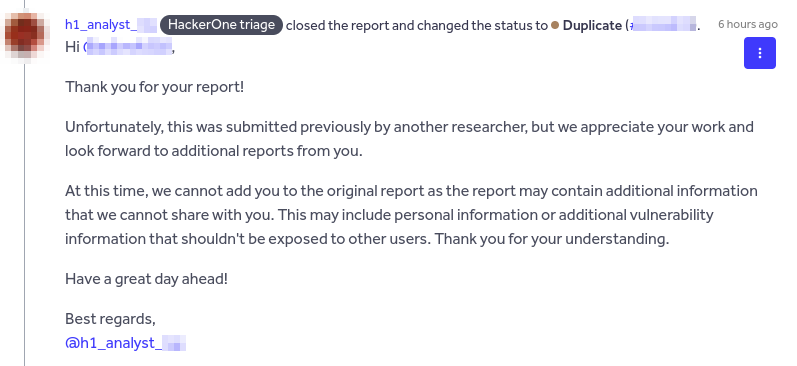
Screenshot: HackerOne triage activity and preliminary review acknowledgment.